50% of all web-applications are vulnerable to at least one serious exploitable vulnerability
Events from the past year and the ongoing Log4j fallout have put application
security at the forefront of all conversations
Find and fixing security problems early in the development lifecycle is more efficient
and cost effective than testing after the application goes into production.
Most companies only test for functional requirements in application testing
but security vulnerabilities should be identified early in the development
phase and through a structured approach.
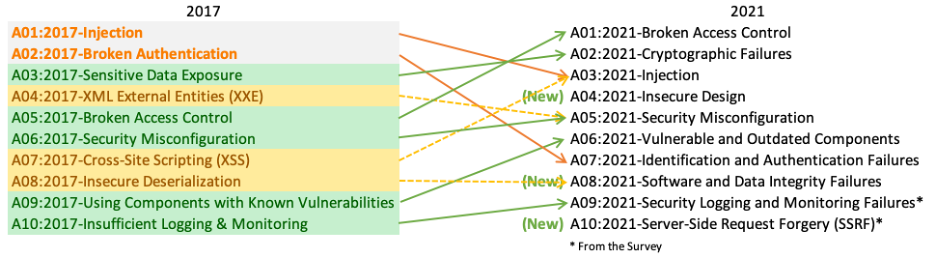
Our Application Security Assessment is designed to meet OWASP Top Ten application security risks.
Key aspects of application security reviews
- Analysis of data access requirements
- Source code analysis
- Understand the business requirements of the applications and how to meet organizational goals
- Conduct a threat analysis of points of weakness in the current SDLC
- Conduct risk analysis and business impact analysis of application weaknesses
- Implementing security into the current SDLC
- Analysis of tools needed to ensure secure code development
- Analyze training regime for secure application development
- Develop a threat analysis and monitoring solution for application security
- Develop policies to address future risk to applications
We review your current application usage, goals for developing new applications,
whether in-house or off the shelf and develop a security strategy. An analysis of
what information you plan to store on systems is conducted, review requirements
to access information and what controls should be in place over application and data
provisioning.